Source Leaked Full Files All Files Instant
Play Now source leaked world-class live feed. Subscription-free on our digital playhouse. Explore deep in a wide array of tailored video lists provided in superior quality, designed for superior streaming fans. With up-to-date media, you’ll always keep abreast of. Explore source leaked personalized streaming in breathtaking quality for a truly enthralling experience. Register for our video library today to browse solely available premium media with 100% free, no recurring fees. Enjoy regular updates and delve into an ocean of singular artist creations intended for choice media experts. Seize the opportunity for singular films—get it fast! Discover the top selections of source leaked bespoke user media with dynamic picture and preferred content.
When source code is leaked, organizations suffer Subscribe now to scan your email for breaches. Learn how leaks occur and how to prevent your proprietary data from being exposed.
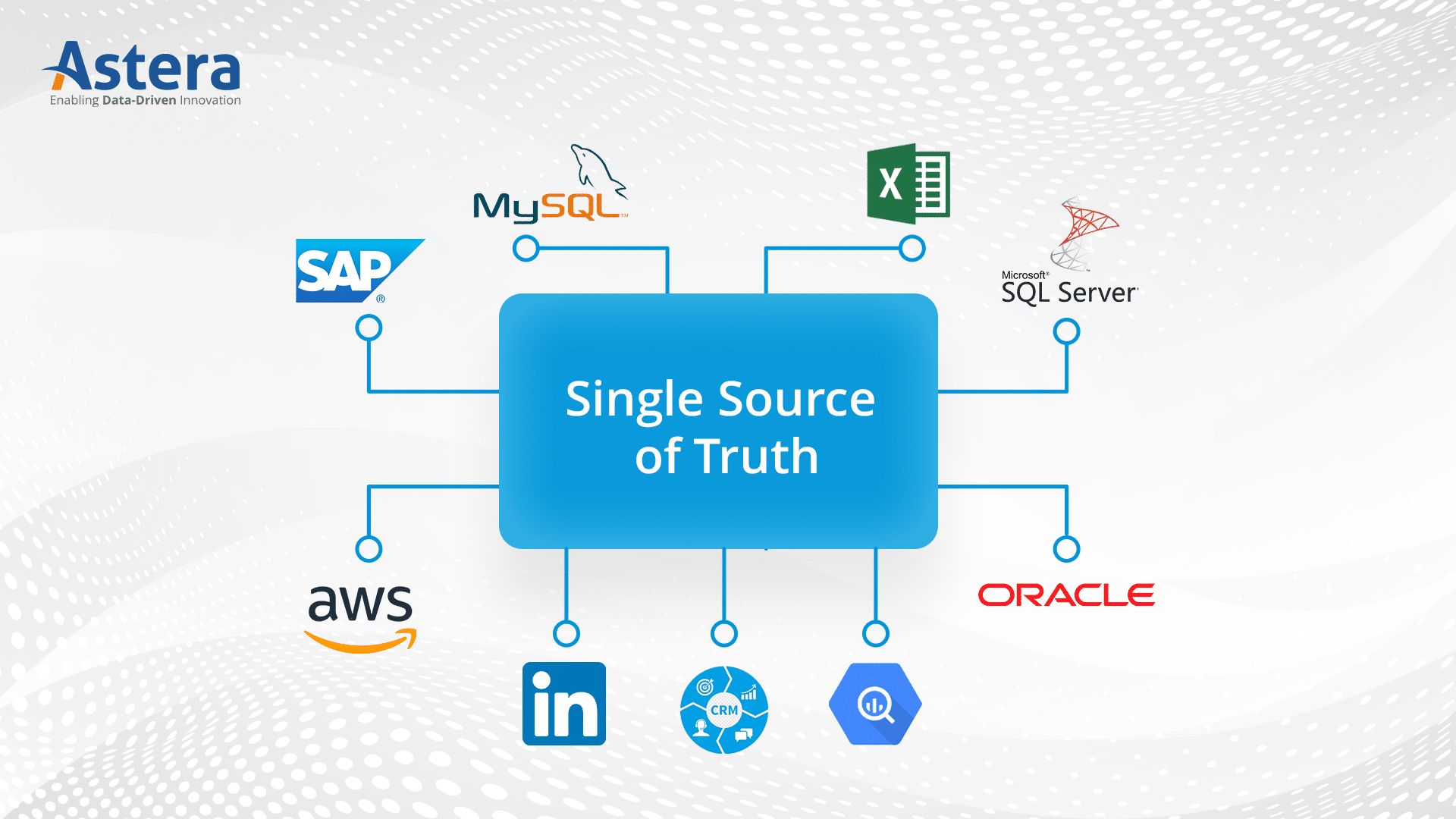
What is a Single Source of Truth (SSOT)? | Astera
Chinese censorship sprang its biggest ever leak on september 11, when researchers confirmed that more than 500 gb of internal documents were dumped online. Get early access to leakedsource 2.0 arriving august 2024 A 500gb leak from geedge networks, a key developer of china's great firewall, exposes the export of mass surveillance and censorship technology.
What is a source code leak
A source code leak is a type of code leak that can expose proprietary information, leading to severe security vulnerabilities and intellectual property theft For example, wiz's state of the cloud 2023 report indicates that 47% of. Modified source engine (2017) developed by valve and leaked in 2020 Discover how code leaks put your business at risk and learn practical steps to protect sensitive source code and maintain security.
Learn how to detect source code data leakage and protect your intellectual property What are source code leaks Source code leaks refer to the process in which the source codes of proprietary applications are made available to unauthorized persons or the public domain for various reasons This might happen in several scenarios, including when information is leaked through public repositories, hacking attacks, internal threats, or when it is posted in version control systems.